Table of Contents
ToggleSOC2 controls : Everything You Need to Know!
Introduction
In the world of Information Technology, there are a lot of buzzwords and acronyms that you don’t understand. As someone who’s interested in security, you want to make sure that the people managing your data are competent. The good news is that there’s a standard called SOC2 [Systems and Organisation Controls 2] that provides guidelines for how companies can manage their Information Technology Systems so they can be trusted by customers. This article will introduce you to SOC2 Controls and how it can help your company to improve information security.
SOC2 Controls List (Define the types of controls)
The SOC2 framework is an effort to define the quality of controls applied to information systems. It provides an objective, third-party attestation of the controls implemented by a Service Organisation, most often in response to explicit requests from customers or regulators. SOC2 controls are defined in the Trust Services Criteria, which is a standard published by the AICPA. The Trust Services Criteria [TSC] are the detailed specification that provides guidance on how these controls should be designed and implemented.
The SOC2 Controls List is based on the five Trust Service Criteria [TSC] which are:
- Security: The Security Service Criteria specifies the requirements for establishing and maintaining a security program to protect data against accidental or malicious loss, alteration, or destruction. This includes the implementation of security controls to ensure that only authorised individuals have access to data and systems. The TSC also addresses encryption methods and tools, as well as disaster recovery planning.
- Availability: The Availability Service Criteria specifies the requirements for providing and maintaining a level of service that is adequate to satisfy agreed-upon performance objectives. This TSC addresses backup and recovery procedures, business continuity planning, incident management processes, and capacity planning.
- Processing integrity: This TSC addresses the integrity of data and systems to prevent or detect unauthorised modification, deletion, or disclosure. This control maximises usability and availability so that the information retained is reliable for its intended use. This service criterion considers how information is encrypted and protected against unauthorised access. It specifies the requirements for ensuring that actions taken by users of information systems are consistent with business processes and policies. The TSC addresses data validity, sequence numbering, and privacy protection.
- Confidentiality: This TSC addresses the confidentiality of information. It specifies the requirements for ensuring that only authorised users have access to data, and that information is not disclosed to unauthorised parties even when an attacker can compromise a system. This service criterion considers how data is protected against unauthorised access by specifying controls over user authentication, session hijacking prevention, encryption, and secure communications.
- Privacy: This TSC addresses the privacy of information. It specifies the requirements for ensuring that individuals are not identified or monitored by unauthorised parties, even when an attacker can compromise a system. This service criterion considers how data is protected against unauthorised access by specifying controls over user authentication and session hijacking prevention as well as encryption to protect data at rest and in transit. It addresses how a system protects the identity of individuals, including their name, address, and other personal information. This criterion also addresses how systems protect sensitive group information such as health and financial data.
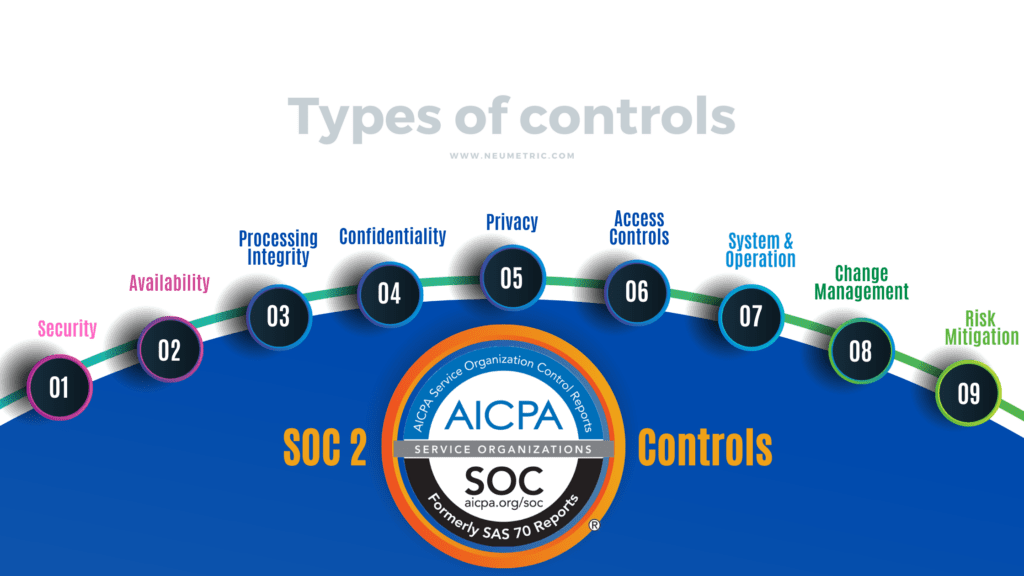
SOC2 Framework derives the SOC2 Controls from the Committee of Sponsoring Organisations of the Treadway Commission [COSO] framework and describes four additional controls. They are:
- Logical and Physical Access Controls: In order to prevent unauthorised access, or modification of data, it is important to implement logical and physical access controls. Logical access controls are rules which define who can have access to what information and when they can have it. These rules should be enforced by a security policy that determines what type of authentication will be required (such as passwords or biometrics). Physical Access Controls are implemented by physically restricting the location where data is stored as well as who has access to it . Physical Access Controls can include security policies that limit where data is stored and who has access to it. They also include physical locks on doors, security cameras, and other mechanisms that prevent unauthorised access.
- System and Operations Controls: System and Operations Controls are implemented through policies that determine how data is accessed, modified, and shared. They include security policies that specify how sensitive information should be handled as well as operational procedures that dictate the steps required to access or modify data. They also include technical controls that are used to protect data, such as firewalls, encryption and monitoring tools.
- Change Management Controls: Change Management controls are implemented through policies that determine how changes to information systems should be managed. They include security policies that specify the process used to change data and operational procedures that describe how changes are made. They also include technical controls, such as backups and disaster recovery plans, which are designed to protect against data loss or misuse of the data during a system collapse. It includes such things as the frequency that information is reviewed, such as once a year or once a quarter, standard operating procedures for reviewing and approving changes, and special instructions for handling specific circumstances.
- Risk Mitigation Controls: Risk Mitigation Controls are designed to make sure that the Organisation does not lose or mishandle sensitive data. They include policies that specify where information is stored, what business functions it is used for, and what physical devices hold it. They also include technical controls such as security firewalls and encryption of files.
The SOC2 audit evaluates the effectiveness of your cloud security controls against those standards that you have chosen. The framework itself is not prescriptive, and so the exact list of SOC2 controls will vary from one Organisation to another; it’s incumbent on businesses to come up with their own lists. The SOC2 controls you must implement will depend on the SOC2 requirements you wish to satisfy.
What are SOC 2 Requirements
The SOC2 requirements are based on the standard itself. The standard outlines the principles and practices that you need to follow in order to successfully perform a SOC2 audit. It’s not prescriptive, however, so businesses can choose their own policies and procedures as long as they meet the requirements of the standard. For example, if your business wants to retain an independent auditor to verify its controls against those specified in SOC2 controls list, then you will have to implement some form of control over access privileges for your cloud assets.

Some of the SOC2 controls requirements include:
- Security management system is in place
- Security policies are documented and communicated to all employees
- Audit trails are in place and working properly
- Access to data is restricted
- Data backups are in place
- Data is encrypted
- Controls are implemented for disaster recovery and business continuity
- Controls are in place to ensure physical security of the data centre
- Controls are implemented for system integrity and availability
- Audits are conducted regularly to ensure compliance with the standards
How can Neumetric help you?
Neumetric is a cybersecurity products and services Organisation specialised in helping Organisations achieve SOC 2 Reports, ISO 27001 Certifications, EU GDPR Compliances, etc. Neumetric has a team of Cybersecurity Experts who can help you to achieve your SOC 2 Report by implementing all the required SOC2 controls and implementing them in a manner that is commensurate with your business needs.
Neumetric can help you implement an effective Information Security Management System [ISMS] that will meet the requirements of a SOC 2 Report. Neumetric can help you conduct regular internal audits to assess your security posture and conduct employee awareness programs to help your employees understand the importance of information security. To know more about Neumetric’s ISO 27001 Certification, SOC2 Report and GDPR Compliance services, please contact us at [email protected].
Conclusion
The SOC2 framework provides a set of control objectives for service providers and their customers. It’s important to understand what these controls are and how they work, so you can protect yourself from fraud or other malicious activity.
FAQs:
Who Does SOC 2 Apply To?
The SOC 2 framework applies to any company that offers cloud-based services. This includes Software as a Service [SaaS], Infrastructure as a Service [IaaS], Platform as a Service [PaaS] and managed security services. The SOC2 certification is also mandatory for any company that wants to sell or provide data centre hosting services.
How many SOC2 controls are there?
SOC2 is made up of 5 trust service criteria (TSC) which totals to 64 individual criteria rather than controls. They are implemented to meet or exceed a specific standard requirement as its name implies — it’s easier simply to think of the 64 individual criteria as requirements themselves.
What are SOC 2 control objectives?
The control objectives are the specific goals that a company must meet in order to be certified. These are the five Trust Service Criteria that SOC2 encompasses. They are:
- Security
- Availability
- Processing integrity
- Confidentiality
- Privacy


