Table of Contents
ToggleIntroduction
In today’s rapidly evolving digital landscape, organisations face an increasing number of cyber threats that can compromise their sensitive data & disrupt business operations. To combat these challenges, Managed Security Operations Centers [SOCs] have emerged as crucial components of cybersecurity strategies. A Managed SOC is a centralised unit equipped with advanced technologies, specialised personnel & robust processes to monitor, detect, analyse & respond to security incidents.
This Journal aims to explore the benefits & features of Managed SOC services. By delving into its capabilities, such as continuous monitoring, threat intelligence & incident response, we aim to shed light on how Managed SOC services empower organisations to enhance their security posture & effectively mitigate cyber threats.
Understanding Managed SOC
A Security Operations Center [SOC] serves as a centralised hub that combines people, processes & technologies to monitor, detect, analyse & respond to security incidents in real-time. SOC teams are responsible for ensuring the overall security of an organisation’s critical assets & data. They perform functions such as log analysis, threat intelligence, incident response & vulnerability management.
Managed SOC services involve outsourcing the security operations to a specialised provider. These providers employ skilled security professionals who work around the clock to protect organisations from cyber threats. They utilise advanced security tools, threat intelligence & analytics to provide continuous monitoring & rapid incident response. Managed SOC services alleviate the burden of establishing & maintaining an in-house SOC, allowing organisations to focus on their core competencies.
While an in-house SOC requires significant investments in infrastructure, hiring & training security personnel, Managed SOC services offer a cost-effective alternative. By leveraging the expertise & resources of a dedicated provider, organisations can enhance their security posture without the burden of maintaining an in-house SOC. Managed SOC services provide access to specialised skills, advanced technologies & 24/7 monitoring, ensuring comprehensive security coverage.
Benefits of Managed SOC Services
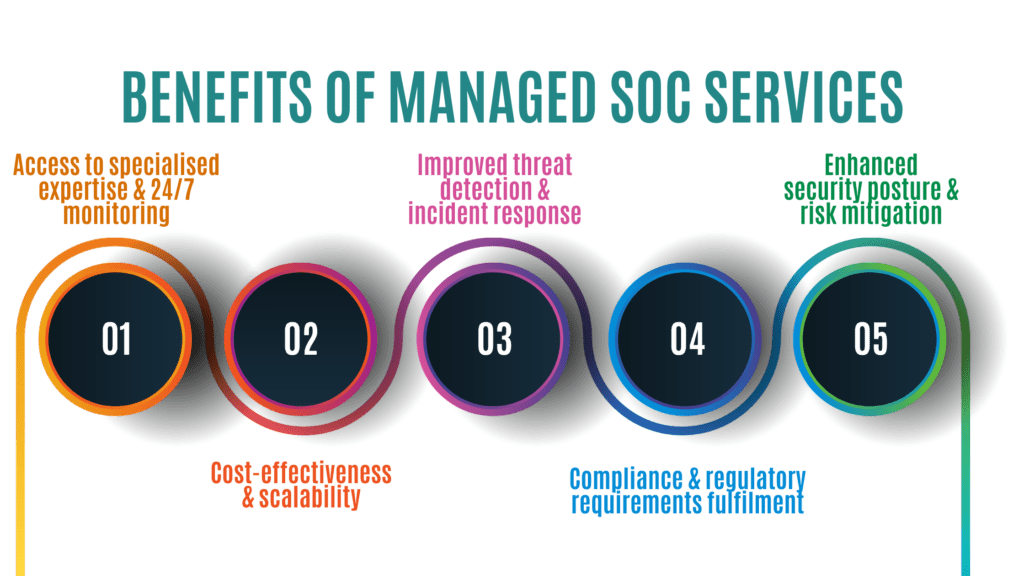
The Benefits of Managed SOC Services are as follows:
- Access to specialised expertise & 24/7 monitoring: Managed SOC services provide organisations with access to a team of security experts who possess extensive knowledge & experience in dealing with cyber threats. These professionals offer round-the-clock monitoring & can swiftly respond to incidents, ensuring a timely & effective response. By leveraging their expertise, organisations gain a competitive edge in detecting & mitigating emerging threats.
- Cost-effectiveness & scalability: Outsourcing security operations to a Managed SOC provider eliminates the need for upfront investments in infrastructure & personnel. Organisations can leverage the provider’s resources on a scalable basis, adjusting their security requirements as needed without incurring substantial costs. Managed SOC services offer a predictable cost structure, allowing organisations to optimise their security budgets.
- Improved threat detection & incident response: Managed SOC teams employ advanced technologies such as Security Information & Event Management [SIEM] systems, Intrusion Detection Systems [IDS] & advanced analytics. This proactive approach enables the detection of threats at an early stage, minimising their impact & potential damage. Rapid incident response & containment are crucial in preventing data breaches & minimising business disruption.
- Compliance & regulatory requirements fulfilment: Managed SOC providers often have a deep understanding of industry regulations & compliance requirements. They assist organisations in implementing appropriate security controls, conducting audits & generating compliance reports, reducing the risk of penalties or reputational damage resulting from non-compliance. Managed SOC services ensure that security measures align with regulatory frameworks & industry best practices.
- Enhanced security posture & risk mitigation: By leveraging the expertise of Managed SOC providers, organisations can strengthen their security posture & mitigate potential risks. The continuous monitoring, analysis & response capabilities offered by Managed SOC services ensure that security incidents are identified & resolved promptly, minimising the impact on the organisation’s operations. By proactively addressing vulnerabilities & security gaps, organisations can reduce the likelihood of successful cyberattacks.
Key Features of Managed SOC Services
The key features of Managed SOC services include:
- Continuous security monitoring & threat intelligence: Managed SOC teams provide round-the-clock monitoring of an organisation’s networks, systems & applications. They leverage Advanced Threat Intelligence to proactively identify potential threats & stay ahead of emerging attack vectors. Continuous monitoring allows for real-time visibility into the organisation’s security posture & enables rapid incident response.
- Incident detection, analysis & response: Managed SOC services include the detection, analysis & response to security incidents. SOC teams investigate & triage alerts, ensuring that genuine threats are promptly addressed while minimising false positives. By following established Incident Response Procedures, Managed SOC providers can efficiently contain & mitigate the impact of security incidents.
- Security event log management & correlation: Managed SOC providers manage & analyse security event logs from various sources, correlating events to identify potential threats. This helps in identifying patterns & indicators of compromise, enabling effective incident response. By centralising & analysing security logs, Managed SOC services can identify & respond to potential security breaches in a timely manner.
- Vulnerability management & patching: Managed SOC services often include vulnerability management, where they assess & prioritise vulnerabilities, ensuring that systems & applications are patched & protected against known vulnerabilities. By regularly scanning & remediating vulnerabilities, Managed SOC providers help organisations maintain a secure environment.
- Security incident reporting & communication: Managed SOC teams provide comprehensive reports on security incidents, including incident details, impact analysis & recommended remediation measures. They communicate effectively with the organisation, enabling informed decision-making & response planning. Clear & timely communication ensures that organisations have a complete understanding of the security landscape & can take appropriate action.
Choosing the Right Managed SOC Provider
Some key factors to consider when selecting the right Managed SOC provider:
- Identifying your organisation’s specific security needs: Organisations should assess their unique security requirements & define their expectations from a Managed SOC provider. This includes factors such as industry regulations, data sensitivity & the organisation’s risk tolerance. A clear understanding of these needs helps in selecting a provider that aligns with the organisation’s objectives.
- Evaluating the provider’s expertise, experience & certifications: It is crucial to evaluate the expertise, experience & certifications of Managed SOC providers. Look for providers with a proven track record, relevant industry certifications & a strong reputation in the market. This ensures that the provider has the necessary skills & knowledge to meet the organisation’s security needs effectively.
- Assessing the technology & tools utilised: Compatibility & integration with existing security infrastructure is important. Assess the technology stack & tools used by the provider to ensure they align with your organisation’s requirements & provide seamless integration. The provider should leverage advanced security technologies & stay updated with the latest industry trends.
- Understanding service level agreements [SLAs] & support options: Review the Service Level Agreements [SLAs] offered by the provider, ensuring that they meet your organisation’s needs. Consider the support options available, including incident response times, escalation procedures & communication channels. It is essential to have clarity on the level of support & responsiveness the provider can offer in case of security incidents.
- Considering scalability & future growth requirements: Choose a Managed SOC provider that can scale with your organisation’s growth & evolving security needs. Assess their flexibility to accommodate future expansion, additional services & emerging threats. A provider that can adapt & grow alongside your organisation ensures long-term partnership & continuous security improvements.
Implementing Managed SOC Services
Implementing Managed SOC services requires a strategic approach to ensure a smooth transition & effective integration with your organisation’s existing security infrastructure. Here are the key steps involved in implementing Managed SOC services:
- Onboarding process & initial assessment: The onboarding process typically involves an initial assessment of the organisation’s security infrastructure, goals & requirements. This helps in customising the Managed SOC services according to the organisation’s specific needs. The provider conducts an in-depth analysis to understand the existing security landscape & identifies areas for improvement.
- Customization & configuration based on organisational requirements: Managed SOC services should be customised & configured based on the organisation’s security requirements. This includes defining Incident Response Procedures, configuring monitoring thresholds & tailoring reports. The provider should work closely with the organisation to ensure that the services align with its unique security objectives.
- Integration with existing security infrastructure: Efficient integration with the organisation’s existing security infrastructure is crucial. This ensures seamless information sharing, eliminates gaps in security coverage & maximises the effectiveness of the Managed SOC services. The provider should collaborate with the organisation’s IT teams to integrate the Managed SOC seamlessly into the existing security ecosystem.
- Training & collaboration with internal teams: Collaboration between the Managed SOC provider & internal teams is essential. This includes training internal staff on Incident Response Procedures, facilitating knowledge transfer & establishing clear communication channels. The provider should conduct training sessions to enhance the organisation’s security awareness & foster effective collaboration.
- Ongoing monitoring, analysis & reporting: Once implemented, Managed SOC services should provide continuous monitoring, analysis & reporting. Regular review meetings with the provider should be conducted to evaluate performance, address concerns & make necessary adjustments. Ongoing monitoring ensures that the organisation remains resilient to evolving cyber threats.
Challenges & Best Practices
- Common challenges in implementing & managing a Managed SOC: Organisations may face challenges such as integrating with legacy systems, managing false positives & aligning the Managed SOC with organisational processes. These challenges can be overcome through proper planning, collaboration & ongoing communication. It is important to set realistic expectations & establish a strong partnership with the Managed SOC provider.
- Best practices for successful deployment & utilisation: Implementing Managed SOC services requires a strategic approach. Best practices include defining clear goals, establishing metrics for success, conducting regular assessments & fostering a strong partnership with the Managed SOC provider. Regular communication, continuous improvement & alignment with business objectives are key to deriving maximum value from Managed SOC services.
- Collaboration between the organisation & Managed SOC provider: Effective collaboration between the organisation & the Managed SOC provider is crucial. This includes sharing relevant information, conducting joint Incident Response exercises & maintaining open lines of communication. The organisation should provide the Managed SOC provider with the necessary context & insights to enhance the effectiveness of Security Operations.
- Continuous improvement & adaptation to evolving threats: Cyber threats are constantly evolving & organisations must stay ahead. Continuous improvement & adaptation involve regularly assessing the effectiveness of Managed SOC services, updating security strategies & incorporating new technologies & methodologies. The Managed SOC provider should stay updated with the latest threat landscape & proactively suggest improvements to enhance the organisation’s security posture.
Conclusion
In conclusion, Managed SOC services offer numerous benefits & features that enhance an organisation’s cybersecurity posture. With continuous monitoring, threat intelligence, incident response capabilities & vulnerability management, Managed SOC ensures proactive protection against evolving cyber threats. Proactive cybersecurity measures & round-the-clock monitoring are vital in today’s threat landscape, where cyberattacks are increasingly sophisticated & prevalent.
To combat these threats effectively, consider Managed SOC as a valuable security solution. It provides specialised expertise, advanced technologies, cost-effectiveness, scalability & compliance with regulatory requirements. Partnering with a trusted Managed SOC provider strengthens security defences, improves threat detection & incident response & safeguards valuable assets & data.
Embracing Managed SOC services is a strategic investment in securing the digital future of an organisation. It empowers proactive identification & mitigation of threats, allowing organisations to focus on core operations with confidence. Prioritise cybersecurity with Managed SOC to stay ahead in an era where cyber threats pose significant risks.
FAQs
What is the difference between managed SOC & managed SIEM?
Managed Security Operations Centre [SOC] & Managed Security Information & Event Management [SIEM] serve distinct purposes in cybersecurity. A managed SOC encompasses a broader scope, providing continuous monitoring, incident response & threat intelligence, while managed SIEM focuses primarily on collecting, analysing & correlating security logs & events.
What is the benefit of managed SOC?
The benefit of managed SOC is that it provides organisations with continuous monitoring, threat detection & incident response capabilities. By outsourcing these critical functions to a specialised provider, organisations can enhance their security posture, effectively mitigate cyber threats & focus on their core business operations.
What should I look for in a managed SOC?
When looking for a managed SOC, consider factors like expertise & experience, range of services offered, integration capabilities, incident response procedures & ongoing monitoring & reporting. Choose a provider that aligns with your security needs, offers scalable solutions & has a track record of success in managing security operations.
How do you make a managed SOC?
To establish a managed SOC, you need to follow these steps:
- Define your organisation’s security requirements.
- Select a trusted managed SOC provider.
- Customise the services based on your needs.
- Integrate the managed SOC with existing security infrastructure.
- Collaborate with internal teams for training & incident response.
- Implement continuous monitoring, analysis & reporting.
- Regularly evaluate & improve the managed SOC services for optimal effectiveness.


