Table of Contents
ToggleIntroduction
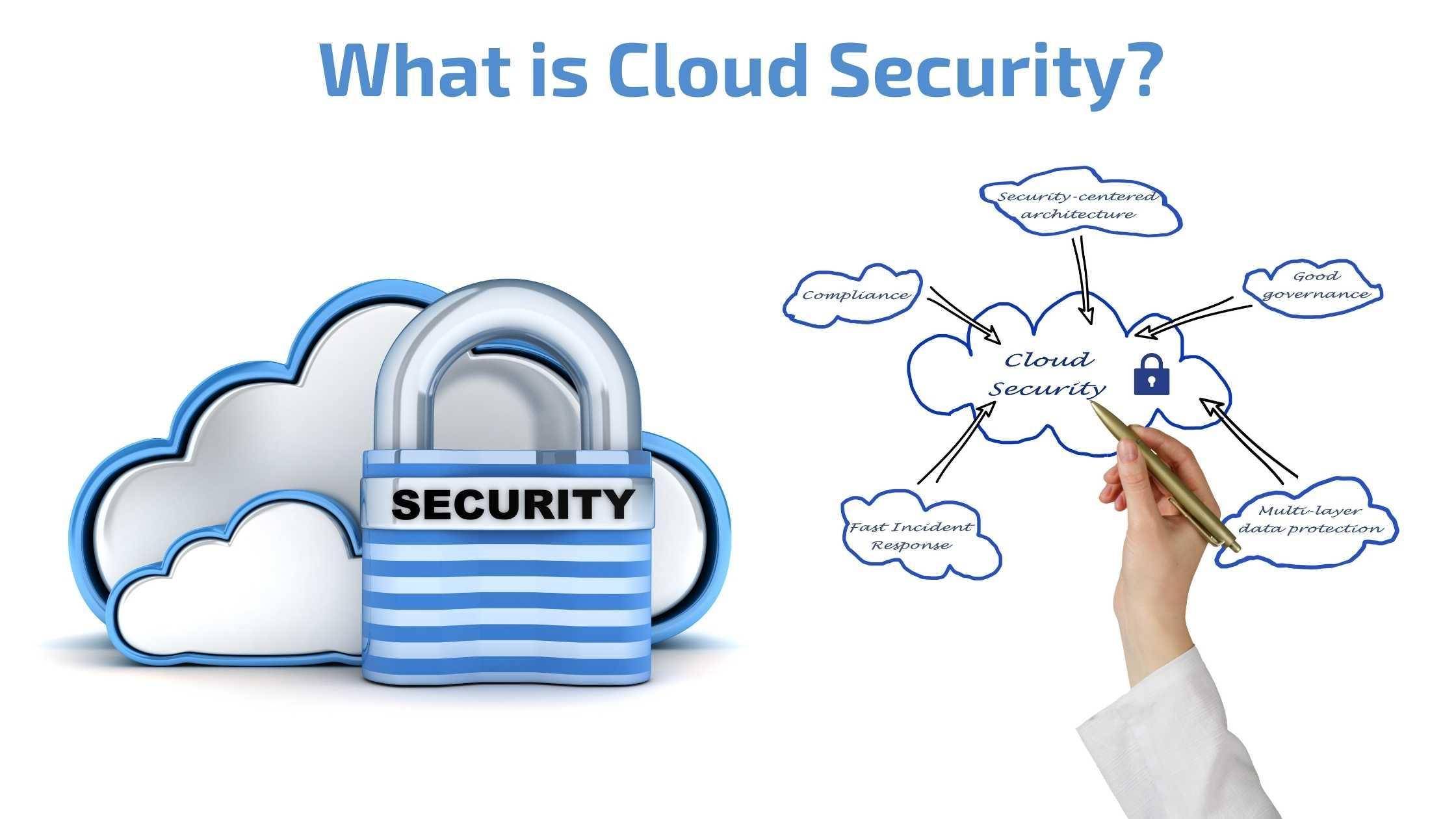
Cloud computing has been hailed as the future of business, with its ability to offer cheaper and more flexible IT solutions. However, there’s no denying that cloud computing also presents new opportunities for cybercriminals to target data and applications. That’s why it’s crucial to understand what cloud security is all about before moving your critical business resources into the cloud. Here, we’ll cover some basic concepts related to cloud security so that you know what protections are at stake when building out a cloud strategy.
Cloud security is the practice of ensuring that data and resources are protected in cloud computing.
Cloud security is the practice of ensuring that data and resources are protected in cloud computing. Cloud security is an extension of information security, and it covers the adoption, implementation, and operation of any service that resides in a cloud computing environment.
Cloud Security is an umbrella term that encompasses many different aspects of information security. Cloud security includes not just technical measures (i.e., encryption), but also non-technical measures such as user awareness programs for compliance with regulatory requirements like HIPAA or GDPR.
Cloud security encompasses all aspects of information security within a cloud computing environment.
Cloud security is a subset of information security. The term “cloud” refers to any Internet-based services such as software, hardware, and storage. In this context, “cloud computing” refers to accessing shared resources via the internet on-demand as an alternative to purchasing and maintaining individual hardware assets.
Cloud security focuses on five main areas of concern:
- Access control
- Audit
- Compliance
- Governance
- Confidentiality
- Data integrity
- Availability
Access Control: Access control is the process of managing who has access to data and systems. It can be implemented at multiple levels within a cloud computing environment, including the network level and the application level. Security controls are usually layered in order to provide protection against different types of threats.
Audit: Cloud providers are responsible for the security of their infrastructure and must provide a level of assurance that their services can be trusted. This includes an audit trail that documents what activity has taken place within the cloud service provider’s systems, as well as external audits by third-parties to verify compliance with industry standards.
Compliance: Cloud service providers must comply with industry standards, such as ISO 27001/27002 and NIST 800-53. These standards provide a framework for implementing IT security controls that can be audited by third parties. Cloud service providers help organisations ensure the security of their data by providing a set of security controls that are implemented at the network, infrastructure, application and other levels.
Governance: One of the most important aspects of cloud computing is the ability to control your own environment. Cloud service providers offer infrastructure-as-a-service (IaaS), platform-as-a-service (PaaS) and software-as-a-service (SaaS). While this allows organisations to reduce costs by outsourcing some or all of their IT needs, it also means they have no control over what data is stored on Cloud. Service providers must have a governance structure in place to ensure that they are complying with industry standards and contractual obligations. This includes internal controls and processes that are designed to prevent, detect and respond to security incidents.
Confidentiality: Cloud service providers have a legal obligation to maintain the confidentiality of data. This means they must take measures to ensure that their employees and business partners cannot access or view confidential information without permission from the client. The Cloud Security Alliance (CSA) provides a set of best practices for cloud providers to follow called the Security, Trust & Assurance Registry (STAR). These guidelines provide you with assurance that your data is being handled correctly by your provider.
Data Integrity: Data integrity is a measure of the trustworthiness and accuracy of your data. Cloud service providers have an obligation to ensure that your data remains intact throughout its lifecycle. This means taking steps to ensure that the data is not corrupted, lost or stolen. In order for you to be sure that your data won’t be damaged in any way, the provider should provide you with some type of assurance plan that outlines how they handle issues when they arise.
Availability: The availability of cloud service providers is an important consideration when choosing a provider. You want to make sure that your data is backed up, stored and secured in such a way that it will be accessible at any time you need it. A good cloud service provider should provide you with access to their platform 24/7. Cloud service providers should be available 24 hours a day, 365 days a year. This means that you can access your data whenever you need to, even if it’s late at night or on the weekend. The provider should also offer support in multiple languages so that anyone who needs help with their account can get assistance from someone who speaks their language.
Cloud security is the protection of data in the cloud.
Cloud Security is a subset of information security, with many different aspects and levels to consider. The term “cloud” itself can mean many different things, so it’s important to be clear about what you’re talking about when discussing cloud security.